Well the most common method of hacking a naive victim is to convince them to run a virus. Why would they even do that, you may ask, well its simple, they don't know its a virus! These days, viruses come with toolkits that help the evil hackers create them with ease. A simple Google search will reveal the toolkits available that can engineer a virus within seconds. Once the hackers make their virus, they upload it to file sharing websites, blogs, download websites, etc disguised as a legitimate program. Some smarter hackers even bundle their viruses with legitimate programs and trick the user in to believing that they have run the real deal. An example of this can be the setup of a free video converter bundled with a virus that can control your computer, steal your information, etc. Once downloaded, and the single program is run, two programs, the legitimate video converter setup is run, as well as the virus, hence, tricking the user in to believing that they have just opened a safe file.
More advanced techniques of hacking involve leveraging the power of Java. Advanced hackers will often make a Java applet that appears legitimate, but when run, downloads the real virus and executes it. This way the user thinks that they have ran a harmless Java web program, but in reality, the web applet has downloaded a harmful Windows EXE to their computer and opened it! Sounds scary right? Well luckily, XetoWare will discuss how to avoid getting hacked below. When it comes to avoid getting hacked, the first thing that comes to mind is an antivirus program: and we definitely agree. Most users are looking for something free, and so are we. The best free antivirus program currently out there, in our opinion, is AVG. AVG will protect you from about 98% of threats, and is also decently resource effective. An antivirus is required because it not only scans every runnable file before you even open them, but every file at the second they are created! In this way, any threats are scanned and eliminated before you can open even touch them, protecting you from general as well as advanced methods of hacking. But antivirus are just one part of the journey to full protection against hacking. Some hackers will even try to infiltrate your network, attempt to use buffer overflow attacks to inject code in your unaware system. What can you do then? Get a firewall is our answer to that. A firewall readily blocks insecure connections, as well as those that are blacklisted or have a bad reputation. Fortunately, Windows already provides a pretty decent firewall, called, you've guessed it, Windows Firewall. However if you are still in great concern, we suggest purchasing AVG Internet Security for full protection. On the other hand, if you are looking for something cost effective, Avast offers a pretty decent free firewall and internet protection package. Lastly, use common sense. With common sense, you can already filter out 80% of the threats online. That is: Do not go to suspicious, unpopular websites, especially those offering free downloads Do not download unpopular, illegal or suspicious files Do not run Java applets from unpopular websites Do not run anything unless you have downloaded it from a reputable source such as CNET, Softpedia or Microsoft But how do you really know if a program is safe? There must be an easy way right? Yes there is. If you must know if an unpopular file is safe to run or not, upload it to VirusTotal, but make sure unpack it first, if you have downloaded it as a ZIP or RAR. Well, that's it! By reading this article, you have obtained valuable information on how to shield yourself from the great threats of the internet! Stay safe! XetoWare 
When it comes to computer speed, there are so many factors to account, however in this post, we will discuss the bare esstentials that every optimal operating computer needs.
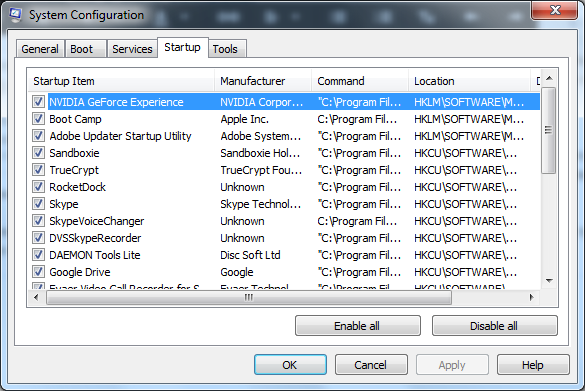
Startup items This is the biggest factor on your computer's speed. 99% of slow computers are clogged with unnecessary start up programs such as 'Yahoo Toolbar Updater' or 'Conduit Search Toolbar', and the more there are, the slower your computer will get. So to figure out which programs you need starting up with your PC and which ones you don't, simply type in 'msconfig' in the Windows 7/8 search box or Windows XP run box and click the 'Startup' tab
Now here's the tricky part: determining which programs you need starting up and which ones you don't. An ideal Windows PC will have nothing checked at startup except its Antivirus and some accessories (ie, Google Drive, Dropbox, Skype). For example, items such as DAEMON Tools Lite, DVSSkypeRecorder, Adobe Updater Startup Utility should not startup with the PC unless it is essential for your purposes.
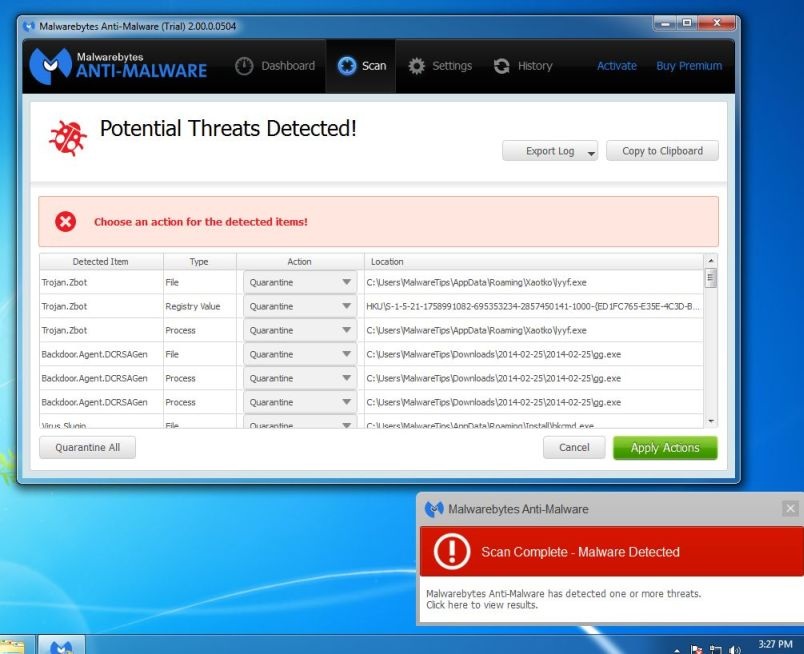
To remove some unnecessary startup items, simply uncheck them in the list and click the 'Apply' button. If you have any trouble deciding if a program is necessary, drop us a note in the comments and we will give you our advice on it. Malware and Viruses Simply put, malware and viruses are just programs that are plain evil. They steal information, may turn your computer in to a bitcoin miner, etc, etc and they slow down your computer. Luckily, there is a solution to this and best of all it is free. Download Malwarebytes Antimalware, a free tool to scan and remove almost all viruses, worms, trojans, malware, etc. Start Malwarebytes and run a 'Quick Scan'. After a few minutes, the program will display a list of potentially malicious items, and all you need to do is click 'Quarantine' to remove them from your computer.
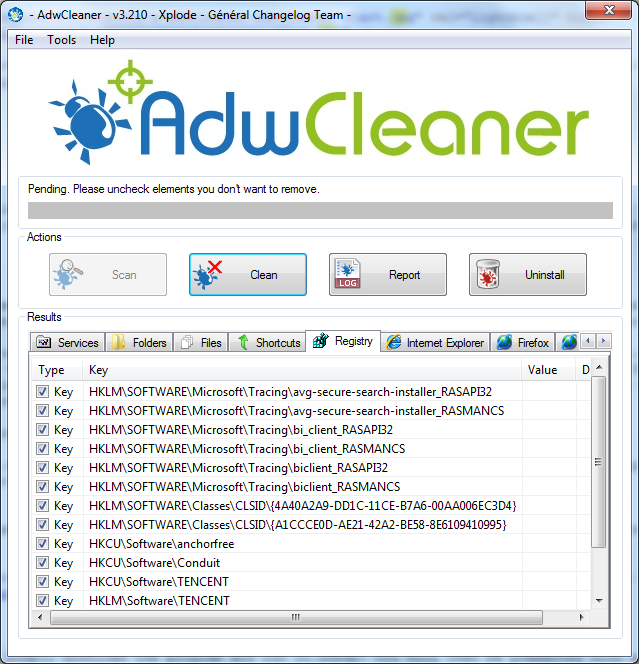
Adware
Although they are not malicious, Adware are plain annoying and hog your computers resources. Adware range from bloated products such as System Optimizer Pro to Conduit browser toolbars. However removing them is easily than you think, instead of going through them manually one by one, there is a much simpler solution: AdwCleaner. AdwCleaner is a simple one-click clean utility. Simply open the tool, scan for adware and click 'Clean'. Unnecessary programs Previously, we have talked about unnecessary startup programs and unnecessary programs are similar, just that they don't startup with your computer, but hogs CPU/RAM usage and slows down your computer. However its hard to decide which programs to remove, but luckily, theres Google. Simply do a Google search of 'is [this program] essential]' and read the reviews posted by previous or current users. Then if it is unnecessary, remove them by opening Control Panel and clicking 'Uninstall a program'. In conclusion, a slow windows pc can be caused a lot of factors, however it is almost always due to the unnecessary startup programs, malware, viruses, unnecessary programs and adware. If you still find your computer running slow, maybe you are using a system that is too new for your hardware if not, drop us a note below and we'll respond with our advice.  So recently, we were trying to do a bit of housekeeping on our software, resigning the code with a valid certificate, fixing grammatical errors; just stuff like that. So when we scanned our Fast Shutdown installer against 60 antivirus engines, we were shocked: one of them detected Fast Shutdown as a 'high risk' threat. Fast Shutdown doesn't do anything malicious. We reviewed the code and analysed all its actions: we didn't find anything that even came close to malicious. So why did AVG detect it as a 'high risk'? After an hour of looking over the code, we decided to use a guess, check and elimination strategy. We removed certain aspects of the program and scanned it against AVG again. After a fair amount of trial and error, we found it: the problem was the icon. How can an icon be malicious? It's just a picture after all. Confused, we consulted AVG, and soon enough they gave us a solution that made enough sense. AVG sometimes uses specific signature points in a file to determine if its a virus: in this case, it was the icon. For example, a previous virus happened to use the same icon as Fast Shutdown, so when AVG scanned our software, they immediately flagged it as a virus. Good strategy AVG, but it could be much better. For example, what virus is digitally signed like Fast Shutdown is? If you ask us, determining if a file is a virus based on its icon is a bit absurd. What if a photo you took on your vacation was detected as a 'high risk' threat?  Hello techies, In the world of software development, there will always be a line between legitimate and untrusted software and that line is called code signing. Code signing dates back to the 1990s when Microsoft first released a object orientated version of Windows. Certified authorities such as COMODO, Microsoft and Thawte generate code signing certificates to individuals and organisiation. The problem is that these companies require indivuduals and organisations to verify their identity through a complex and tedious process requiring the presentation of phone bills, driver licenses, phone call verifications, proof of address and the list goes on. Furthermore, indivudual developers are especially disadvantaged as they cannot choose a custom alias to represent their software: the certificate must display their name. This can lead to privacy concerns, especially when your real name is displayed to all users of your applications. VerifyMyApp is XetoWare's newest innovation, aiming to help individual developers and small businesses increase credibility to their software and apps by offering a cost-effective company code signing to their applications. VerifyMyApp skips identity verification and instead relies on application verification: scanning it against 60 antivirus and antispyware engines as well as testing it ourselves on real computers to evaulate the files and settings that your app creates, modifies or removes. This service will filter out untrustful software, increase the credibility of legitimate applications and present them as programs to other businesses, end users, software distribution websites and antivirus software. For more information, visit VerifyMyApp's official website. |

 RSS Feed
RSS Feed